NERC on Monday laid out a framework for transmission planners (TPs) and planning coordinators (PCs) to include cybersecurity in their planning studies to address a “rapidly evolving threat landscape [of] increasingly sophisticated cyberattacks” against the North American power grid.
The Cyber-Informed Transmission Planning white paper is rooted in the 2021 ERO Risk Priorities Report, in which industry stakeholders rated cybersecurity among the greatest risks facing the electric grid. (See Grid Transformation, Cybersecurity Lead 2021 ERO Risk Report.)
With new generation sources and remote-control technologies making up a larger proportion of the grid, experts have warned of a growing “attack surface” that increases the grid’s vulnerability to malicious cyber actors.
The new white paper aims to fulfill a suggestion in NERC’s 2023 Work Plan Priorities that the ERO Enterprise “develop cyber-informed planning approaches … to study, identify, and reduce the number of critical facilities and attack exposure/impact” by promoting the integration of security considerations with utilities’ transmission planning tasks.
“While the electric industry is improving, many organizations have minimal collaboration and coordination between their engineering and security staff in a truly integrated manner,” NERC said in the white paper. “Neither side needs to become an expert in the other discipline; however, there are likely opportunities where increased collaboration and integrated processes can drive better business decisions, cyber-resilient long-term transmission plans, and enhanced [grid] reliability and security.”
Road Map to Reliability
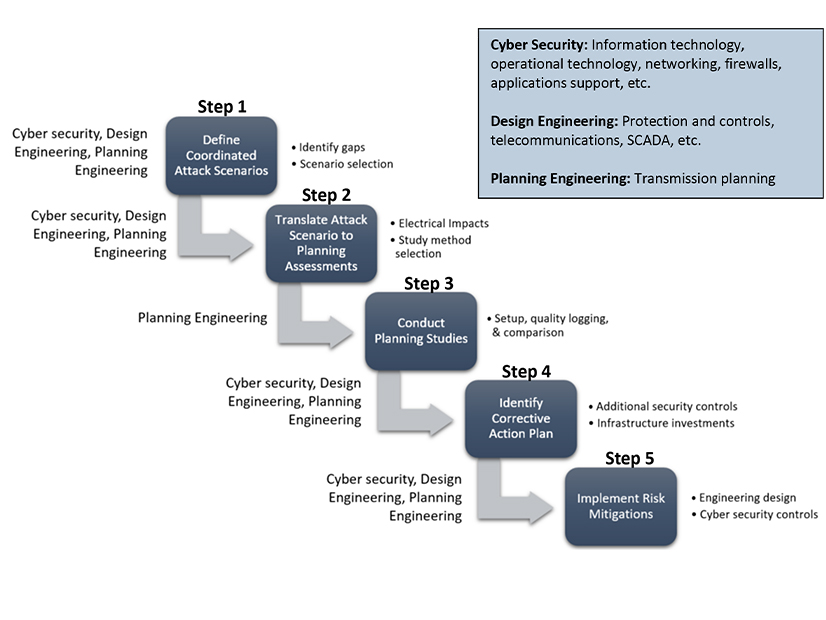
In the first part of the white paper, NERC outlined a “road map” by which TPs and PCs can integrate cybersecurity professionals into their planning process to ensure that cyber risks are accounted for. This strategy took the form of a Cyber-Informed Transmission Planning Framework (CIPTF), a five-step process in which planners and cyber experts:
- define scenarios for a coordinated cyberattack, particularly involving multiple elements with common security gaps;
- determine grid elements that might be affected in each attack scenario;
- conduct studies to analyze the potential performance of the identified elements under attack;
- analyze outcomes of the planning studies and determine what mitigations might address the identified reliability issues; and
- implement those mitigations and any other security controls to neutralize the identified risks.
NERC provided a list of scenarios as a sample of the type of situation that TPs could study, while stressing that “there are likely other scenarios … worth of study” based on each entity’s particular circumstances. The ERO’s examples included an outage of multiple distributed energy resources due to compromise of a common manufacturer and outages of multiple transmission substations due to compromise of devices through remote access capabilities.
In addition to the framework, the white paper’s second chapter discusses how the ERO can contribute to security integration.
First, NERC could further integrate cybersecurity into the definition of “adequate level of reliability” (ALR), a term used in the Federal Power Act to specify what standards the ERO can develop and enforce. While the current ALR definition — which NERC is responsible for developing — does mention “cybersecurity events” and “malicious acts,” the report’s writers urged the ERO to revise this description to explicitly include security as a critical component of reliability. They also suggested the addition of an ALR performance objective to ensure that adverse impacts are managed properly.
Along with updating the ALR definition, the paper proposed revising reliability standard TPL-001-5.1 (transmission system planning performance requirements) to address two “shortfalls.” First, according to the current version of the standard, studies of cyberattack impacts only have to address scenarios involving the loss of two generating stations. The paper observed that attacks on multiple stations, “while less likely,” could pose a serious threat to reliability and should be included in studies.
Second, TPL-001-5.1 currently has no requirement for utilities to mitigate any adverse grid performance issues identified; entities are only required to study these issues. The paper presented this as a significant weakness and suggested that a revised standard “encourage” mitigation steps, though did not discuss how this requirement might be put into practice.
In a statement, Mark Lauby, NERC’s chief engineer, said the CIPTF “sets the stage to plan for a more resilient and secure system, addressing the risk in the long-term planning horizon rather than attempting to bolt on security later in the future.” He added that the integration of cybersecurity enhancements could help “to reduce the number of critical stations on the bulk power system.”

