NERC’s GridEx VIII security exercise highlighted multiple areas for improvement for grid reliability, including better communication within and outside the electric industry, heightened security around drones and reduced reliance on data centers, according to the after-action report from the Electricity Information Sharing and Analysis Center.
The E-ISAC hosted the biennial exercise Nov. 18-20, 2025, and included a distributed play portion and an executive tabletop. In the distributed play, held the first two days, participants from 378 organizations worked individualized exercises based on a core scenario developed by the E-ISAC.
The tabletop, held Nov. 20, brought together leaders from 84 organizations, including industry executives, senior government officials and other “entities impacted by the scenario.”
Scenarios for the tabletop and distributed play involved a conflict between two fictional nations in which adversary “Crimsonia” invaded ally “Beryllia” and launched cyber and physical attacks against U.S. and Canadian infrastructure to delay and degrade their response.
The tabletop occurred in summer 2028 across three acts. In Act 1, Crimsonia imposed a naval and air blockade on Beryllia, while electric utilities noticed spikes in cyber probes and forced oscillations across the Eastern and Western Interconnections.
Act 2 occurred several weeks later and involved steps by Crimsonia to deter intervention by rendering GPS services “essentially unavailable,” causing power outages at “U.S. and Canadian facilities with military missions,” and attacking Microsoft identity and authentication services. Act 3 involved physical sabotage against water systems, drone attacks on a nuclear power plant and a ransomware attack on a pipeline.
The distributed play took place in 2026 against the backdrop of preparations for a global sporting event dubbed the “World Chalice.” Play comprised five moves occurring over the course of two weeks.
-
- Move 0 (before play began) — Utilities suffer vandalism and theft in the lead-up to the games, while the E-ISAC reports a new strain of malware being used on electric infrastructure overseas.
- Move 1 — A small-scale cyberattack against corporate computers distracts information technology personnel, leading to a major attack on electric and gas utilities that disrupts monitoring and control systems.
- Move 2 — Large-scale attacks are carried out against multiple substations with drones and firearms. An electrician is held hostage at one facility. Additional attacks affect defense-critical infrastructure (DCI) as Crimsonia invades Beryllia.
- Move 3 — A heat dome causes failures at multiple data centers, affecting digital infrastructure including cloud services. Adversaries cut telecommunication lines to control rooms, insider attacks occur at utilities and vendors, and utility staff receive faked messages from leadership.
- Move 4 — Players discuss the long-term recovery efforts from the perspective of a week after the last move.
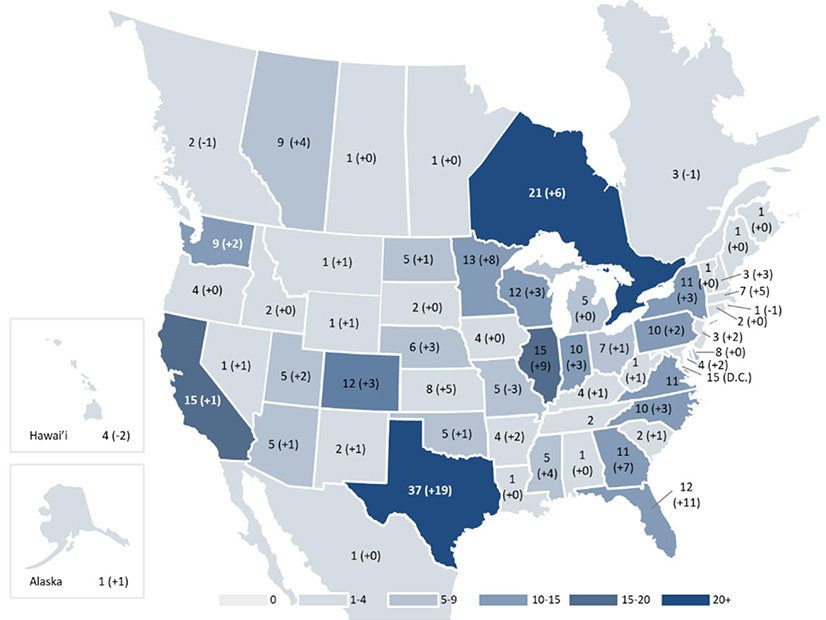
With 378 organizations participating, the distributed play portion of GridEx VIII was the biggest since GridEx V in 2019 and the third largest since the first exercise in 2011. NERC explained the attendance shifts since GridEx V — 293 organizations participated in GridEx VI and 252 in GridEx VII — as likely due to registration policy changes. Since GridEx V, only E-ISAC members and partners have been able to register for the exercise, but in GridEx VIII asset owners and operators could vouch for non-members for the first time.
Most participants were based in North America, with additional involvement from entities in Australia, Germany, Portugal and New Zealand. 63 participants were based in the footprint of SERC Reliability, more than any other regional entity and 15 more than in GridEx VII; WECC had the second-most participants at 60, four fewer than in GridEx VII when it was the leader.
Recommendations
The tabletop and executive play sessions generated a list of recommendations to improve reliability and resilience.
Recommendations from the tabletop included that U.S. and Canadian defense facilities work with industry to develop “collective understanding of the electric reliability requirements for DCI and associated risks to” defense-critical electric infrastructure. Participants also urged government entities to improve information sharing with industry and promote laws like the Cybersecurity Information Sharing Act of 2015 and programs like the E-ISAC’s Cybersecurity Risk Information Sharing Program.
The drone-related incidents prompted a recommendation that the U.S. and Canadian governments work with industry on responses to drone threats and “clarify available government support.” Participants also suggested that industry and government discuss how to shield utilities from liability for following government directives affecting their operations or energy and resource allocation.
Distributed play participants urged that industry continue to coordinate with government and emergency management partners on exercise and response planning, and encouraged entities to continue testing their various communication methods for potential failure modes. Contributors also suggested that entities practice their internal coordination and communication along with strengthening their external relationships.