In a required annual update to FERC on cybersecurity incidents on the electric grid, NERC reported only a single incident occurred in 2025 that met the ERO’s reporting requirements, down from three the previous year (RM18-2).
However, NERC suggested that rather than being a vindication of the ERO’s cybersecurity policies, the lack of additional incidents may indicate that reporting requirements need to be tightened to improve awareness of cyber threats.
Reliability standard CIP-008-6 (Cybersecurity — incident reporting and response planning) requires electric utilities to report qualifying cybersecurity incidents to the Electricity Information Sharing and Analysis Center. (See FERC OKs Cyber Reporting Rule.) Reportable incidents are defined in the technical rationale for the standard as those that compromise or disrupt:
-
- a cyber system that performs one or more reliability tasks of a functional entity;
- an electronic security perimeter of a high- or medium-impact grid cyber system; or
- an electronic access control or monitoring system of a high-impact grid cyber system.
Reports must include the intended effect of the cyber incident, the attack vector of the incident and the level of intrusion the attacker achieved or attempted. They may be submitted through the E-ISAC portal, the NERC EOP-004 reporting form or the Department of Energy’s DOE-417 form. NERC must submit an anonymized summary of the reports to FERC each year, according to FERC Order 848.
To submit a commentary on this topic, email forum@rtoinsider.com.
The ERO’s cyber incident report for 2025, released March 20, was light on details. The reporting entity was not identified beyond being in the SERC Reliability region. NERC also did not specify when the incident took place.
NERC did disclose that the incident involved a single medium-impact grid cyber system, which an unidentified intruder attempted to compromise through “connection attempts to multiple external interfaces from a single internet protocol … address.” The attacker did not gain access to the system because network perimeter controls blocked the connection requests, and the target entity activated its cyber incident response plan.
No operational impacts were reported from the intrusion. NERC reported that there was no impact to grid reliability and “the controls in place were effective in identifying and mitigating the attempt to compromise.”
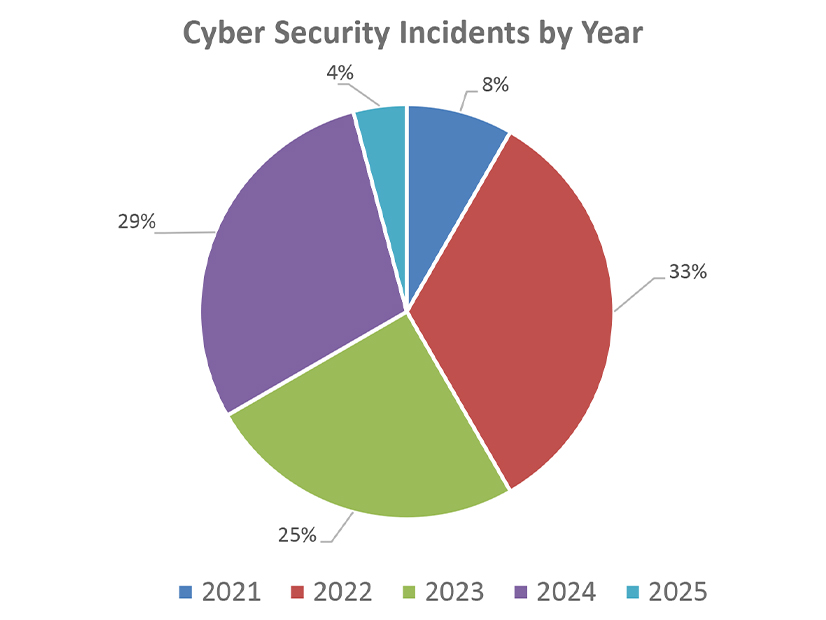
The single incident report collected in 2025 was the lowest since NERC began its annual reporting in 2022. That year, the ERO reported two cyber incidents to FERC that occurred in 2021; subsequent annual reports outlined eight incidents in 2022 and three each in 2023 and 2024. (See ERO Says 2024 Cyber Incidents Showed Increased ‘Sophistication’.)
The ERO wrote in the most recent report that the number may have decreased because of “the subjective criteria to define attempts to compromise,” citing a study it undertook in 2021 to examine registered entities’ implementation of CIP-008-6. The report’s writers mentioned that Project 2022-05 (Modifications to CIP-008 reporting threshold) is underway to clarify the type of events that qualify under the standard.
“NERC is encouraged that there were no reliability impacts from the reported incident … and that the [responsible] entity reported the attempt to compromise to the E-ISAC,” NERC wrote. “However, the diminished number of reports … reinforces the importance of establishing criteria that [do] not rule out attempts to compromise from being reported simply because no harm to, or intent to harm, a [grid cyber system] was identified.”